Debian, Ubuntu, or Mint’s installation instructions still include information on how to use OpenPGP Web of Trust. It is not worth it to do this from other operating systems, according to our team.
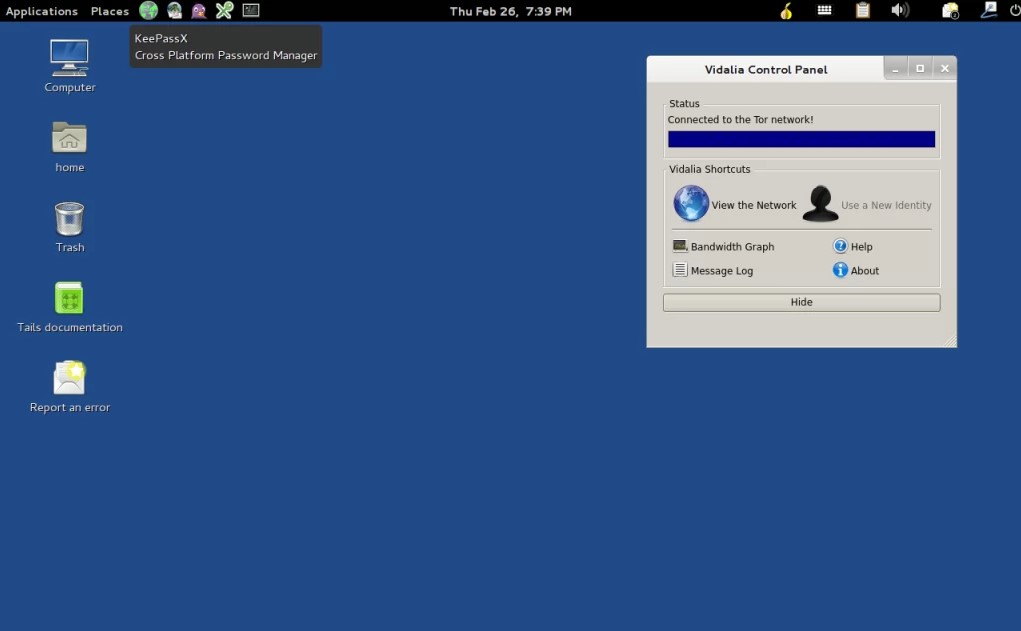
Tails 1
Password 123
Firmware is the BIOS, UEFI, and any other software that is stored on an electronic chip of the computer. Every operating system, including Tails, depends on firmware for starting and running. Therefore, no operating system can defend against a firmware attack.
Operating systems are dependent on their firmware, just as a car is dependent on the quality road it drives on. Tails can be hacked if one of our mirrors is compromised and is serving malicious files. An adversary with the ability to analyze traffic timings and patterns could be able to deanonymize Tor users. End-to-end correlation attacks are used to describe these attacks. The attacker must simultaneously observe both ends of the Tor circuit. It is less likely that the verification failed due to malicious downloads from our mirrors, or because of an attack on your local network. Both verification methods can help protect you against malicious downloads from our mirrors, but they cannot protect you against a compromise to our website. While it is possible to protect your computer from some firmware attacks by keeping it in a safe place, other firmware attacks can also be done remotely.
These advanced OpenPGP skills would need to be learned elsewhere. Hardware alterations are more common on public computers, internet cafes, libraries, and desktop computers. It is easier to conceal a device on these computers. If the physical components of your computer have been modified, it could be compromised. Because the list of Tor exit nodes is public, sites you visit may know you use Tor. Verification also fails if you attempt to verify a different version of Tails 4.21.
You can try a manual upgrade if Tails does not start after an automated upgrade. An anonymity network that is used for fast connections such as browsing the internet or instant messaging cannot protect 100% against end-to-end correlation attacks. VPNs, which do not use three independent relays, are less secure than Tor in this instance. Tor Browser and Tails both include tools like HTTPS Everywhere to encrypt the connection from the exit node to the destination server whenever possible. Tails sessions can be used for multiple purposes at once, so an adversary could link all your activities. Most likely, the verification failed due to an interruption or error during the download. OpenPGP doesn’t have any instructions for how to verify downloaded files.
Download Tails
Tails make use of the Tor network to help protect your privacy online. We keep a list of issues that could affect Tails’ last release, as no software is perfect.
Tor and Tails are not designed to make you look like anyone else on the Internet. Instead, they will make all Tor and Tails users appear the same. It is impossible to tell who is among them.
We have not heard of any attempts to anonymize Tails users who use Tails for different purposes. Tails use Tor because it is the most widely used network to prevent surveillance and censorship. Tails or any other software or operating system cannot protect you against everything, even if they try. Don’t lose time if your download is not complete or damaged due to an error in the downloading process. Tails can be downloaded for free. Independent security researchers can also verify our work.
Tails can be restarted between activities to prevent an adversary from linking your activities. You can restart Tails while you check your work email or your whistleblowing mail. JPEGs and other image files often include information about the location and camera used. Use a different browser to verify the download. Try downloading from another mirror if the download fails.
What is a portable operating system?
You can manually upgrade your Tails operating system to fix any problems. You should not transfer files to or to Tails USB sticks from another operating system.
Parents can block Tor connections that aren’t using Tor bridges because they are subject to parental controls and Internet service providers. You might be concerned that files stored in Persistent storage could be used to link activities, so you can use a Tails USB stick for each activity. You could use one Tails USB Stick for activism and one for journalism.
Tails 0.23 forgot this and, even though they didn’t explicitly specify them in that release, they defaulted back to the previous values. This makes it possible to change the defaults in the future. Tails 2.0 will be focused on sustainability and maintenance.
You should make sure that your OpenPGP keyserver configuration is updated if you have GnuPG keys stored on Persistence before Tails 4.1. Also, adapt Tails to the new changes. If you have too much RAM, fix the link to the system requirements documentation page. Always use a trusted operating system to install Tails. Tails can be downloaded on a safe computer or copied from a friend. Tails will protect you against malware and viruses on any operating system. Tails are independent of any other operating system.
Tails 1 System Requirements
- Memory (RAM): 1GB of RAM required.
- Hard Disk Space: 1GB of free space required.
- Processor: Intel Pentium 4 or later.