Use the command resmon to find the processes creating the issue. Even if you have serious issues, instead of installing Windows it is recommended to take steps to fix the installation, or for Windows 8, by executing the command DISM.exe Online / Cleanup-Image Restorehealth. If you encounter any difficulties with the executable, verify its authenticity prior to eliminating snooper.exe.Get More Softwares From Getintopc
Snooper Tool
Password 123
SharkFest participants sharpen their skills at analysis through lectures and lab-based workshops presented by the most experienced professionals in the field. Wireshark key code contributors meet during the conference to enhance and improve the tool in order to keep its value in the efficiency of today’s networks. Once it detects a sound from the microphone recording will begin immediately. This feature can be configured in any way you like and it’s very convenient.
Snooper Tool Feauters
Not all great Windows applications have the Verified Signature label and they don’t have any poor ones. There is also the option of downloading an update (3.6.0rc1) and the accompanying documentation. If you’re at an office or shared network, you may request the administrator of your network to run a scan on the network to find out if there are any malfunctioning and infected equipment.
If you’re on an individual connection, such as at home, it is possible to conduct an anti-virus scanning on your gadget to be sure it’s not infected by malware. When I installed Lync 2013 RTM I discovered there was no Lync Logging Tool isn’t available. As you can see in the following the tool is not available when you search for the tool in Server 2012, it is not listed in the list of applications. The laws regarding how to use this program differ from country to country.
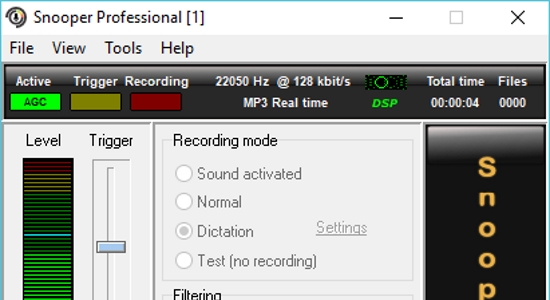
The Snooper audio recording tool is able to be used to record a variety of kinds of recordings. A snooper is a simple tool for recording audio that allows you to record sounds for many different uses. Check out a replay from the 2016 and 2017 Packet Trenches series and gain access to Hansang’s traces file.Participate with Gerald Combs, Hansang Bae, Kary Rogers, Sake Blok Jasper Bongertz, Christian Landstrom, Phill Shade, and numerous other experts in packet analysis at SharkFest which is an engaging Wireshark experience of training. Wireshark is the most powerful and most widely used analysis of network protocols.
It allows you to see the network’s activity on a micro-level and is the standard norm for numerous non-profit and commercial enterprises including government agencies, as well as educational institutions. Wireshark growth is made possible by the voluntary contributions of networking experts from all over the world. It is the result of a work begun in 1998 by Gerald Combs 1998.
Snooper is also able to remove any unwanted noise from recordings, as per the recorded noise profile, and even encrypt sound files to ensure privacy. If you’ve ever had to find the ability to make audio recordings, you’ll understand that it’s crucial to locate an excellent sound recording application to accomplish the task.
How to Get Snooper Tool for Free
Keep track of the time and the location where the snooper.exe erro is crucial information for solving. Furthermore, the nature of the virus can influence the removal of snooper.exe. In this instance, you should activate the Safe Mode with Networking. It is an environment that is secure and disables all processes and loads only the necessary drivers and services. In Safe Mode, you are able to use security software and conduct a thorough system analysis. We’d like you to know that from time to time it is possible to not be aware of a potentially dangerous software program.
I have noticed that snooper comes with an earlier version number, however, there is no information on the changes made. Clean and tidy computers are among the most effective ways to stay clear of issues when using Microsoft Lync Server 2013, Debugging Tools.
This includes conducting malware scans, cleaning your hard disk using cleanmgr and SFC/scannow, uninstalling any programs you no longer require, keeping track of any auto-start programs, and turning on auto Windows updates. Make sure to make regular backups or establish the recovery points. “* “snooper.exe has encountered a problem and needs to close. We are sorry for the inconvenience.” If you notice that the “Verified Signer” status of an application is listed as “Unable to Verify”, you need to take a closer to examine the process.
To remove this snooper.exe virus, install and download full security software such as Malwarebytes. It is important to note that not all software is able to detect all types of malware, and you might need to test different options before you’re able to succeed. It’s not recommended to download replacement executable files from websites for downloads, as they could contain viruses, etc. If you are required to download or install snooper.exe We recommend reinstalling the primary application that comes with it Microsoft Lync Server 2013, Debugging Tools.
Another method to avoid seeing this site in the future is to utilize Privacy Pass. All trademarks and registered trademarks that appear at oreilly.com are the sole property of the respective owner. This means that a legitimate software is incorrectly flagged as malicious because of an excessively broad detection signature or the algorithm used in antivirus software.The logo and name that are part of Softonic is a registered trademark of SOFTONIC International S.A. Alongside an easy-to-use screen, Snooper provides a variety of nice alternatives, such as post-recording sessions. When you’ve completed your recording, for instance, you can request it to be immediately sent via email. The best part is that Snooper utilizes a small MP3 format to ensure that every recording you make does not take up a lot of memory on the computer.
According to several sources on the internet According to various sources, 44% of users have removed this file. So it is likely to be harmless However, it is advised to verify the authenticity of this executable on your own to determine if it’s secure or is a virus. The most effective way to determine if these are suspicious files is to conduct a thorough system scan using Reimage. If the file is categorized to be malicious, those programs will also eliminate snooper.exe and remove the malware that is associated with it.To keep delivering you malware-free catalogs of applications and programs Our team has added the Report Software feature in every catalog page. It transmits your feedback to us. You can keep track of which applications running on your computer, even when you’re not there. The Power Tool runs invisibly and generates the record file (snoop.log) which tracks the start and stop of each program.
It can be used to spot the presence of tampering, or simply to keep track of the time in every program. We suggest you test this brand new program that corrects computer problems, guards from malware and optimizes your computer for efficiency. This software fixes various computer issues and protects you from things like malware, file deletion, and hardware malfunctions.
We do not recommend or endorse the use of this software when it is in breach of the laws. Tom keeps up-to-date on industry trends and posts updates and his views on his blog Microsoft Teams Podcast, his blog, and the email list.Following the release of the key health Indicators in Skype for Business 2019, The Skype for Business Server 2019 Debugging Tools has been updated. First launched to support SfBS 2019, in the month of November of 2018 These are a set of additional tools that can be used by IT Admins to aid in the troubleshooting of Skype in Business Server 2019 deployments.
It is not recommended to remove a safe executable or safe file without a reason, since this could alter the performance of associated software that uses the file. Keep your programs and software current to avoid any future issues caused by damaged files.
Regarding problems with the functionality of the software, you should ensure that you are checking driver and software updates frequently so that there’s a low or any chance of problems developing. If you believe you might be suffering from an infection, you should attempt to eliminate the issue immediately.
Snooper Tool System Requirements
- Operating System: Windows XP/Vista/7/8
- Memory (RAM): 512MB of RAM required.
- Hard Disk Space: 100MB of free space required.
- Processor: Intel Pentium 3 or later.