Therefore, we suggest using an alternative OSX SDK version for building VeraCrypt. To generate MSI applications, WiX Toolset v3.11 must be installed. If successful, there will be newly created VeraCrypt binaries located in the ‘ReleaseSetup Files directory. Select x64 as your active platform and then build the solution once again. Get More Softwares From Getintopc
Veracrypt
Password 123
The freeware software can be downloaded for free and without time limits. The freeware software can be downloaded at no cost for professional and personal use. The build requirements and directions are similar to Linux however make must be used in place of make. This means that legitimate software is incorrectly identified as malicious because of an excessively broad detection signature or the algorithm used by an antivirus program. Dcs_tpm_owner_02.pdf refers to the configuration of TPM to enable EFI System encryption. Correct the wrong language in the installer when the user chooses an alternative language to English and then chooses English after pressing OK on the language choice dialog.
Veracrypt Features
In the event of creating a volume on a current hard disk, choose the desired size of the drive as well as the volume password and format to start. Once you’ve completed it you can make use of the main interface for VeraCrypt to install the encryption in the volume container to be a drive on Windows. So all .sys files that are part of the official VeraCrypt binary files are digitally signed using the digital certificate of IDRIX that was issued by the GlobalSign certification body. Make sure to keep this in mind when you are able to compile VeraCrypt and test your binaries to official binaries. If your binaries are not signed then the size of official binaries will typically be around 10 KiB more than the size of your binaries.
Although VeraCrypt is extremely powerful it’s not designed for casual users. You’ll need a thorough knowledge of computers for installing and using the application. Look for unsafe settings and passwords as well as suspicious add-ons and outdated software. The software is not available for download. It could be because of the program’s discontinuation due to a security flaw or any other reason. It’s highly likely that this program is infected with malware or has bundles of software.
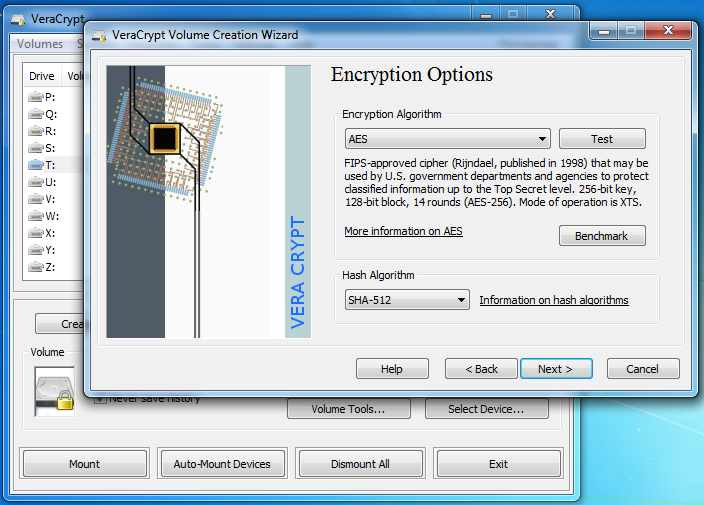
Encryption is a process that can be made faster by hardware with modern processors. Encryption is automatic, real-time(on-the-fly) and transparent. This improved security adds delays only for the opening up of encryption partitions, without any impact on performance during the application usage phase. This is fine for the legitimate owner, however, it makes it much more difficult for attackers in gaining access to encrypted data. The enhanced security adds a delay to an opening process for encrypted partitions, without any impact on performance in the application usage phase. This is fine for the legitimate owner but makes it more difficult for attackers to gain access to encrypted data. This increases the security of the algorithms that are used to create system and partitions encryption. This makes it resistant to advancements in brute force attacks.
If you’ve any sensitive data on your computer You should secure it. With a tool such as VeraCrypt, it is easy to secure partitions or create files that can be mounted as drives within Windows. Demo versions offer limited function for free however, they charge for a more advanced set of options or the elimination of ads from the program’s interfaces. In certain cases, it is possible that all functions are restricted until the license has been purchased. Demos usually aren’t time-bound, but their functionality is restricted. Secures a whole partition or storage device, such as the USB memory stick or hard disk.
BlockedIt’s very likely that this program is infected with malware or has unneeded software. Beware that this program could be harmful or may include unwanted software that is bundled. It is a good idea to regularly encrypt your files so that you don’t have to worry about data leaks in the future. If you’re always scared of sharing your personal information online, Internet, and sharing your personal information, make sure to secure your data today.
How to Get Veracrypt for Free
The program is lightweight, but the security it provides is significant. The trial software permits users to test the program for a short time. After that time, the user is able to decide whether to purchase the software or not. While most trial software programs are time-bound, there are some that have limitations on features. For more details, look over the legal notices that are attached to the code source. CleanIt’s very likely that the program is free of viruses.
It also resolves a number of security vulnerabilities and security problems that are found in TrueCrypt. The first step is to create an environment variable called ‘WSDK81 that points towards the Windows SDK for Windows 8.1 installation directory. The batch file will assume that the certificate for code signing was issued by GlobalSign. If the certificate you have is issued by a different CA Then you must place the intermediate certificates of that CA in the “Signing” folder and modify sign.bat in line with the certificate’s requirements. This increased security will only add an additional delay in opening encrypted partitions, without any effect on the performance of the application. In this way, it’s acceptable to the legitimate owner however, it makes it more difficult for hackers to gain access to the encrypted information.
VeraCrypt is a free software to encrypt disks. It is built on TrueCrypt. This is fine for the legitimate owner of the data, however, it is a challenge for attackers to access encryption data.
We do not support or support any use or usage of the software when it is in breach of the laws. The download will continue on the official VeraCrypt website. VeraCrypt is able to solve a number of problems that other alternatives like TrueCrypt or DiskCryptor are not able to solve. VeraCrypt also has advantages in speed thanks to its huge number of encryptions per iteration. Repair some instances related to the “Parameter Incorrect” error during EFI the system encryption wizard. Most commercial software and games are designed to sell or for an economic purpose. It is automated, in live-time (on-the-fly), and completely transparent.
Veracrypt System Requirements
- Operating System: Windows 7/8/8.1/10
- Memory (RAM): 1 GB of RAM required.
- Hard Disk Space: 50 MB of free space required.
- Processor: Intel Dual Core processor or later.