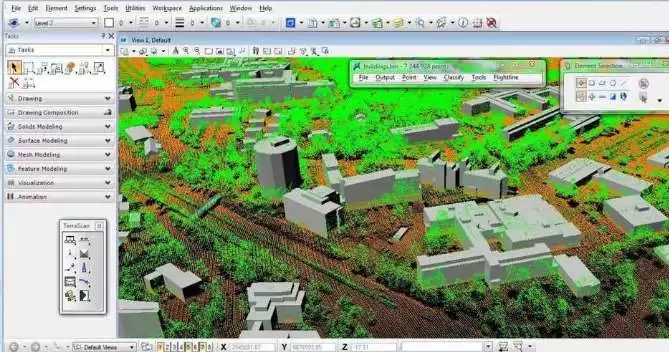
TerraScan is the primary application of the Terrasolid Software family for managing and processing different types of cloudy points. It includes the ability to import and structure projects to handle the huge amount of points generated by a laser scanning mission and the trajectory data. Different classification algorithms allow for an automatic process of filtering the cloud of points. The automated process makes sure that the entire pipeline from the development phase to the end-user machine is safe and aligned. Built on advanced automation, Terrascan can also fail the automated build process if there is a significant vulnerability discovered. Find security and compliance violations in Infrastructure as Code to mitigate the risk prior to creating cloud-based infrastructure. Get More Softwares From Getintopc
Password 123
Terrascan
Visit Terrascan’s release page to find the most recent versions of the builds for every supported platform. In Kubernetes YAML, you can set up Terrascan to not skip the policies you want to skip with an annotated, as shown in the following snippet. Learn more about the in-file instrumentation and the configuration document on the documentation website. Terracan could be integrated into CI/CD workflows in order to ensure security best practices are followed. Check out our documentation for integration with your pipeline. Photography in oblique and vertical orientations is accomplished by mounting HD camera systems.
Terrascan Features
The system is able to be used wherever in the world with processing taking place in the cloud system in Israel. The tool can be used to create vectorized wires and identify points on wires that belong to an electric line. It can draw line string components within the CAD file for all wires that are detected. For the most secure and the best experience overall on our website, we recommend the most current version that includes Chrome, Edge, Firefox, or Safari. As a default feature, Terrascan scans your entire configuration for compliance with all policies. But, Terrascan supports the granular configuration of resources and policies. Terracan Labs uses unmanned aerial vehicles to provide photographic mapping, oblique, and stereoscopic aerial photos.
At Accuracy(tm) We envision an environment where businesses can create using cloud computing with confidence. Our goal is to empower companies to attain cloud-based cyber resilience using security designed for developers that self-heals the cloud. The Accuracy platform detects problems with the infrastructure and then contextualizes the results with risks to applications to find breach pathways throughout the development cycle.
It generates code automatically to fix the issue and then implements fixes to the development pipeline. Accuracy lets enterprises large and small attain security for their cloud infrastructures through cloud-based, open-source tools like Terrascan(tm). This comes after the launch of Terrascan’s admission controller. It is which is a new feature that allows you to implement Policy as Code uniformly across the lifecycle of software development. PAC has gained a lot of attention for creating security measures in the development process, which allows the detection of errors in Kubernetes before they go into production. To test the code you are using for security concerns, you can use the below. Terracan has multiple methods to install and is available as an image that can be downloaded from Docker.
It’s crucial for these policies to control deployments at runtime because the production environment may be changed directly via CSP or Kubernetes controller. CSP and Kubernetes controller. The reality is that PC software used to build pipelines as well as in production tends to be quite different and has different configurations, policy libraries, and control/reporting systems. Making use of Terrascan for its role as an IaC scanner, in conjunction with the admission controller in Terrascan, however, it consistently enforces the same policy across the development as well as deployment.
Accuracy allows organizations to safeguard their cloud-based infrastructures in multi-cloud and hybrid cloud environments. It effortlessly scans infrastructure as code for configuration errors, examines cloud infrastructures that are provisioned for any changes in a configuration that can cause posture drift, and allows the reverting back to an insecure posture. Argo is an open-source GitOps engine designed for Kubernetes that is able to synchronize Kubernetes clusters and makes it much easier to define, plan and manage the execution of complex workflows and apps on Kubernetes. Terracan is able to scan repositories to find violations, as well as its connection with Argo, can bring those capabilities into the cluster via automated processes that go beyond the source code and into the controller.
If you wish to download the latest policy it is necessary to go through the initialization procedure. When you are embracing Infrastructure as Code such as Terraform, Kubernetes, Argo CD, Atlantis, and AWS CloudFormation it is essential to ensure that best security practices and compliance regulations are followed. Terracan offers more than 500 standard policies to examine IaC against the most common standards for a policy like the CIS Benchmark.
How to Get Terrascan For Free
It utilizes its Open Policy Agent engine so that you can create custom policies with Rego. Rego query engine. Accuracy is an open-source project. Terracan is integrated with Argo Project. Argo Project to dramatically improve cloud security, as developers embrace the GitOps method of operation. Terracan can be utilized with pre-commit hooks in order to avoid introducing security flaws to your repository. A sample configuration is available in the comment section of the here file within this repository.
Check cloud infrastructures provisioned by cloud providers for configuration changes that can cause the possibility of posture drift and allow for the reverting back to an upright posture. A set of best practices and security tests for static analysis of Terraform code. Make use of the Terracan configuration file to choose the policies that should be excluded or included in the whole scan.
Processing, management of the cloud, and visualization are just some of the features of TerraScan. Additionally, the program includes automated tools to generate 3D vector data based upon these laser-generated points.
The outcomes of the completely automated classification can be improved with half-automatic and manual classification tools in conjunction with a variety of 3D Point Cloud visualization tools. Every rego contains a JSON “rule” file that specifies the metadata of the policy. In default, Terrascan downloads policies from Terrascan repositories when it scans when it is the first time.
The Vegetation Index can be used to differentiate the vegetation hit from ground-level points, particularly in photogrammetric cloud clouds, where the actual ground level isn’t evident. For the most secure and smooth experience on our site, we recommend the most current editions that include Chrome, Edge, Firefox, and Safari.
Manually set up policies that can be wiped out or applied globally by a scan that covers all resources, or for the specific resource. The –find-vuln option to gather the vulnerabilities reported in its registry in Terrascan’s output. At present, Terracan has support for Elastic Container Registry, Azure Container Registry, Google Container Registry, and Google Artifact Registry.
Terrascan System Requirements
- Operating System: Windows XP/Vista/7/8/8.1/10
- Memory (RAM): 512 MB of RAM required.
- Hard Disk Space: 200 MB of free space required.
- Processor: Intel Pentium 4 or later.