Soon after its launch, PGP encryption found its ways outside of the United States, and in February 1993, Zimmermann was the subject of an investigation into criminality conducted by The US Government for “munitions export without having a license”. In the past encryption systems that had keys larger than 40 bits or more were deemed to be munitions in the sense of the US export laws; PGP has not used keys that were smaller than 128 bits, which means it was considered to be in compliance at the time. After a few years, the probe into Zimmermann was concluded without making any criminal charges against him or anyone else. Get More Softwares From Getintopc
Password 123
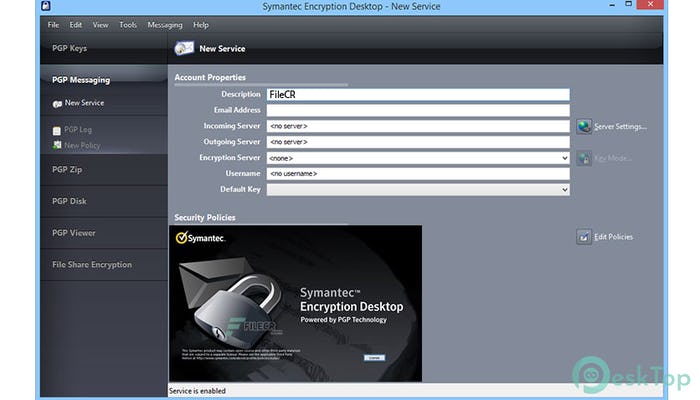
Symantec Encryption
The initial release of the system is called the web of trust. This was to stand out from that of the X.509 technology, which utilizes an approach that is hierarchically built on certificate authority it was included in PGP applications later. The current version of PGP encryption offer options via an automatized key management server. To achieve this, PGP uses a hybrid cryptosystem, which combines symmetric key encryption with public-key encryption.
Symantec Encryption Features
It encrypts the message with an asymmetric encryption algorithm that needs a symmetrically generated key by the sending party. The symmetric key can be used only once, and it is known as the session key. The session key needs to be provided to the receiver to ensure they are able to decrypt the message, however, to safeguard it during transmission, it is encrypted using the receiver’s public key. It is only the key that belongs to the receiver that is able to decrypt the session key and then use it to symmetrically encode the messages.
Townsend Security partnered with Network Associates in 2000 to develop a compatible Version of PGP for the IBM I platform. Townsend Security again ported PGP in 2008 and this time, to the IBM Z mainframe. The version that was released for IBM z PGP utilizes an encryption service that is free in z/OS that makes use of hardware acceleration. Software Diversified Services also offers a commercial version of PGP (SDS E-Business Server) for the IBM Z mainframe. On April 29, 2010, Symantec Corp. announced it was buying PGP in the amount of $300 million, with the goal of the integration of the software into their Enterprise Security Group.
The Viacrypt/PGP team that was reunified started working on the development of new variations of PGP encryption, based on PGP 3. PGP 3 system. In contrast to PGP 2, which was a command-line only program, PGP 3 was designed initially as a library for software that allows users to work either from the command line or within a GUI environment. The initial contract between Viacrypt and Zimmermann Zimmermann team was that Viacrypt would come with even-numbered versions as well as Zimmermann variants with odd numbering. To clear up any confusion regarding the possibility that PGP 3 was the successor to PGP 4, PGP 3 was renamed and made available in the form of PGP 5 in May 1997.
It is also, as you would expect it comes with the ability to wipe data from your computer which can destroy important documents that users would like to eliminate permanently. “How to utilize OpenPGP to secure your emails and save them stored in Cloud storage.” July 22 14th, 2014.
Further and encrypting entire partitions or disks which render the computer unable to boot in the event that someone attempts to hack into the system without permission. The creation of an open-source, OpenPGP-compliant software library called OpenPGP.js that is built-in JavaScript and was endorsed through the Horizon 2020 Framework Programme of the European Union, has allowed applications that run on the web to use PGP encryption inside the browser on the web. The new version of PGP applications utilizes both OpenPGP and S/MIME that allows communications with any user who uses a NIST-specific standard. For enterprises, Townsend Security currently offers an enterprise version of PGP to both the IBM i as well as the IBM z mainframes.
In the initial version in the initial version, it was the RSA algorithm was employed to protect session keys. Security of RSA relies on the single-way function that mathematical integer factoring has. The algorithm for symmetric keys used to secure PGP Version 2 was IDEA which could at some point in the near future be discovered to have previously undiscovered cryptanalytic weaknesses.
How to Get Symantec Encryption for Free
Specific instances of PGP or IDEA security flaws aren’t publicly publically available. Since the current versions of PGP include other encryption techniques, their vulnerability in cryptography differs based on the algorithm being used. But, none of the algorithms currently in use is publically known to have cryptanalytic weaknesses. In this time of turmoil, Zimmermann’s group worked on the development of a new variant of PGP encryption, dubbed PGP 3.
The standard was expanded to include Camellia cipher in RFC 5581, in the year 2009. as well as key exchange and signing are based upon Elliptic Curve Cryptography (i.e. ECDSA along with ECDH) through RFC 6637 in the year 2012. The support of ECC encryption has been added to the RFC 4880bis proposal in 2014. Inside PGP Inc., there still was a concern about patents. RSADSI had a dispute with the extension that its Viacrypt RSA license to the newly formed firm. The firm adopted an informal internal standard, which they referred to as “Unencumbered PGP” which would “use an algorithm without licensing issues”. Due to PGP encryption’s global importance, Many would like to develop their own software that could work in conjunction with PGP 5.
Since the message can be encrypted at any time, modifications within the message will not be able to pass the encryption process using the correct key. The sender employs PGP to generate digital signatures for the message, using either RSA as well as DSA algorithms. In order to do this, PGP computes a hash from plaintext and creates the digital signature using the hash using the private key of the sender.
Downloading a key from a website isn’t an accurate guarantee of connection; intentional impersonation is a possibility. Since its inception, PGP has always included the possibility of distributing public keys as an ‘identity certificate’ that is also encrypted so that any alteration is easily identified. However, just making an unalterable certificate that is difficult to alter without being discovered is not enough. This will only prevent corruption after the certificate is made, not prior to.
It is also essential for users to ensure through any means ensure that the public key contained in the certificate actually belongs to the entity or person who holds it. The public key could be signed digitally by a third-party user to verify the relationship between the key and the person who signed it. There are various levels of assurance that can be provided in these signatures. Although numerous applications read and record this information few of them include this level of assurance when determining whether or not to trust a particular key.
Google will tell you that the file cannot be examined for viruses, however, you can click Download Anyway to get the installation. These steps will show that you the procedure to set up Symantec Encryption Desktop. If it is already in your system, you can follow the steps to install a more recent version on top of your previous version.
In the past, if an encrypted email could not be sent because of some or all recipients with a Key Not Found, the email was bounced. If there is a recipient who has KNF, the message is sent to valid recipients. The user could receive an additional email containing those recipients who have a KNF who the email was not sent. For more information about the previous version of Symantec products in relation to End of Life, see our Symantec Encryption Products End of Life and page.
PGP is used to sign as well as encryption and decrypt messages, e-mails directories, files as well as entire disk partitions to enhance the security of email communications. With Symantec’s proven technology as its base, the Encryption Desktop program relies on user-generated PGP keys to safeguard crucial information which is transferred between email clients as well as the data saved locally on the computer used by the user.
Additionally is that it is able to be used for secure file sharing. It also lets users encrypt or sign data that is opened in windows or in the clipboard. In order to provide unbreakable security for data, it is based upon PGP technology and employs strong public key algorithms like DSA (1024-bit keys, only), RSA (up to 4096-bit keys), and Diffie-Hellman.
For a search of all of the encryption products, return to the main page for download overview and enter “Encryption”. To search for SEMS, which is the Symantec Security Management Server, you’ll want to click “Encryption Management Server”. At the time of writing, the most current Version of SEMS currently is 10.5 (Consult on the “Current Version” article for more information about the latest versions of the various encryption solutions.
It is the PGP Desktop 9. x family comprises PGP Desktop Emails well as PGP Complete Disk Encryption PGP NetShare and PGP NetShare. Based on the software, these products offer digital signatures on desktops, desktop e-mail, IM security, whole disk encryption, file as well as folder encryption, encryption, self-extracting archives, as well as encrypted shredding and destruction of files deleted.
Capabilities are licensed in various ways based on the features needed. As of December 27, 1997, PGP Inc. was purchased from Network Associates, Inc. (“NAI”). NAI was the initial firm to adopt legal export strategies through the publication of the source code. In NAI it was the PGP team also added disk encryption desktop firewalls, intrusion detection, as well as IPsec VPNs in the PGP family of products.
Symantec Encryption System Requirements
- Operating System: Windows XP/Vista/7/8/8.1/10.
- Memory (RAM): 512 MB of RAM required.
- Hard Disk Space: 200 MB of free space required.
- Processor: Intel Dual Core processor or later.