Take our word for it, but take a look at our recovery stories. Prey is not only a reliable Find My iPhone alternative but also the best phone tracker and recovery tool. You will get detailed reports detailing every detail that the police need to find your iPhone. Some reports suggest that the software may be malicious or install unwanted bundled software. These false positives could mean that users should be cautious when installing this software. Get More Softwares From Getintopc
Preyproject
Password 123
The process can take anywhere from 20 minutes up to several hours, depending on the size of the disk and the characteristics of the computer. The device will stop working if it is turned off. It will then resume when it is turned on again. AES_128 can be used for internal fixed drives. XTS_AES128 can be used for removable internal drives such as flash drives.
Preyproject Features
This means that a benign program is incorrectly flagged malicious because of an excessively broad detection signature. Prey helps you find and retrieve stolen or lost computers. Prey is available to help you locate your computer if it has been stolen or lost. You just need to mark the computer as missing on your Prey Control Panel. The system will send reports every 20 minutes. Prey is an Open Source platform that values the privacy and clean handling of user data.
Prey uses the device’s GPS and the nearest WiFi hotspots for triangulation to determine its exact location. It is lightweight, free, and open-source software. The laws governing the use of this program vary from one country to another. If the laws are not in compliance with this software, we do not condone or encourage its use.
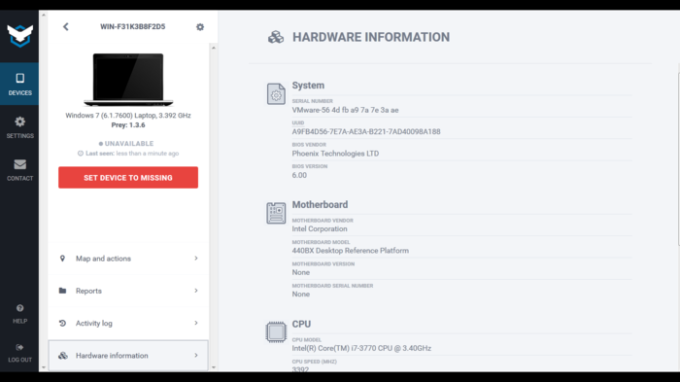
The original version of Prey was first released for Linux and Mac OS X in March 2009, and for Microsoft Windows in April 2009. Prey is currently available for mobiles, tablets, laptops, and desktops running the macOS, Windows, and Linux operating systems. Prey mobile anti-theft security can be used to protect up to 3 devices using a single account. This is done through your account’s web panel. For greater coverages, you can get a free account or check out our PREMIUM plans. It is crucial to know where assets are located at all times. Prey’s persistent device tracking and security solution will help you avoid information loss in remote workers. Prey’s free version allows you to use 3 devices as well as most of Prey’s features.
Our new report will explain how remote work has changed the landscape of investment, cybersecurity, and mobility. You can manage thousands of devices with ease in the enterprise panel. Label your inventory, perform bulk tasks easily, and view all information about your device globally.
This page contains all source code for Prey clients for Mac, Linux, and Windows. Click on a Windows device that was encrypted previously using the same platform to view its individual view. This could be because the program has been discontinued, has a security problem, or any other reason. The file was scanned using VirusTotal, which has more than 70 antivirus software products. No threats were found. This software is safe and clean. We care about your privacy and security. That’s why the OPEN SOURCE code is used.
How to Get Preyproject for Free
You can remotely lock your devices and erase stored passwords using the app. This will ensure that no one has access to your personal information. While selecting ‘Full Disk” takes more time, it protects the entire disk. This option is best for computers in active use. However, choosing the ‘Used Space Only’ will speed up the process but won’t protect any unused space.
Locate a compatible Windows device from your Prey control panel. Click it to open its view. You will find Disk Encryption on the right-hand side action bar.
Select the drives that you wish to encrypt using BitLocker. You simply install a small agent on your phone or PC that waits for a remote signal and then works its magic.
Only your personal data and information are retrieved and used as requested. BitLocker, a native encryption tool, is included with Windows 10 Pro, Enterprise and Education. It doesn’t have to be downloaded or purchased separately. Prey will automatically fetch the latest version from its server and then update it. This saves you the hassle of having to reinstall every time. CleanIt is very likely that this program is clean. These tools simplify management and keep a global inventory of devices. Prey will connect with the Windows device to disable BitLocker and begin decryption on the selected disks.
This software provides a range of features that provide remote security capabilities for theft and loss. This software could be malicious or contain unwanted bundled programs. It is recommended that users look for alternative software and be very careful when installing or using this software. The encryption process takes time as Windows must encrypt all data. The computer’s specs and the size of the disk will determine the completion time. Prey will connect to the device and request BitLocker for encryption to start. Click the action to view a progress bar. Follow the encryption process to protect the drive.
Preyproject System Requirements
- Operating System: Windows XP/Vista/7/8/8.1/10
- RAM: 1 GB
- Hard Disk: 500 MB
- Processor: Intel Dual Core or higher processor