There are many SSH server implementations that are available. SSHD services that require prerequisite resources such as hotkeys and sshd_config, should they not already exist they will be automatically created during the startup process of the service. Once you’ve given your username and password via OpenSSH all the features on the remote computer will be accessible. Get More Softwares From Getintopc
Openssh
Password 123
OpenSSH will turn off the ssh RSA signature scheme in default mode in the next version. The SSH protocol”ssh-RSA” is the signature scheme “ssh-RSA” signature scheme that uses the SHA-1 hash algorithm combination together with the RSA public key algorithm. The algorithm is now able to carry out targeted attacks using the algorithm SHA-1 for less than USD$50k. It is important to note that the removal of “ssh-RSA” signatures does not necessarily mean that you have to stop using them for RSA keys. They are often employed in backup systems, scripts, and configuration management tools as well as by sysadmins and developers. They also have a single sign-on that allows users to change his or her accounts without needing to enter the password each time.
Openssh Features
Don’t run installation programs for Bitvise software that don’t include an official digital signature issued by Bitvise. Bitvise wasn’t the first registered agent of putty.org. We acquired the domain from a previous owner who had used it in ways not connected to the software. We thought it would be useful to use it as you would expect.
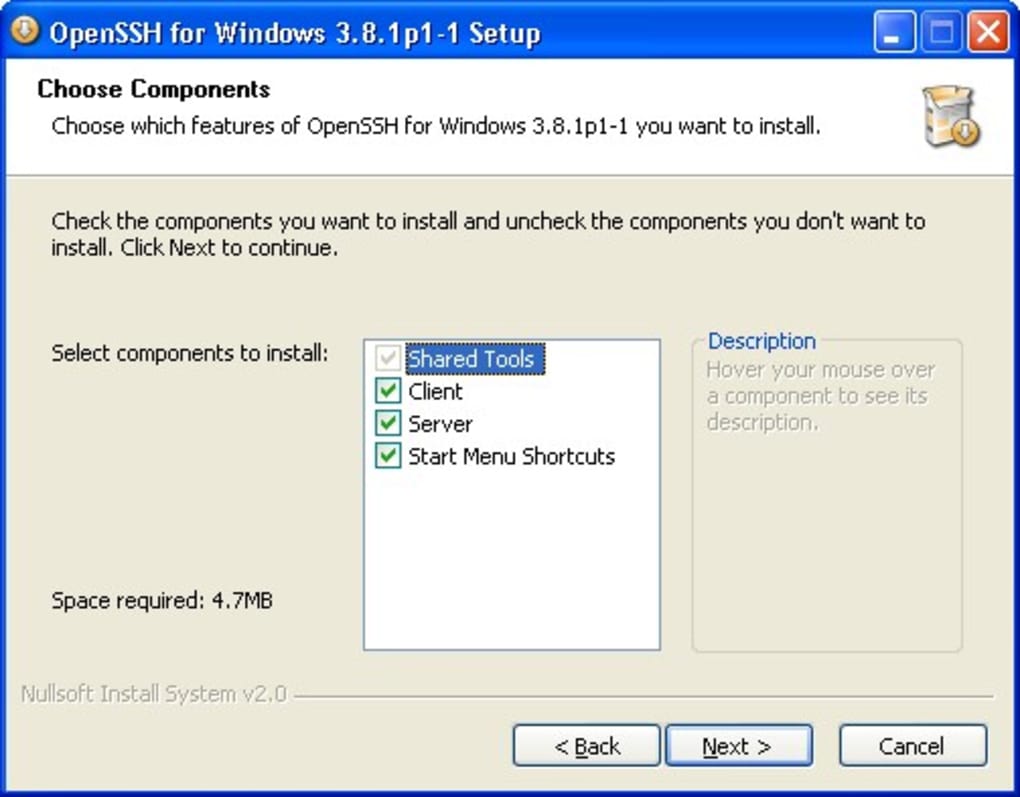
Furthermore, OpenSSH provides a large range of secure tunneling options with a variety of authentication options as well as sophisticated configuration options. Secure Shell is a Secure Shell protocol that was originally created by Tatu Ylonen in the year 1995 as a reaction to a hacking event within the Finnish university network. Microsoft Windows is the world’s most used operating system. With its various versions, it is extensively used in almost every company – both on the desktops of users and on servers in computing centers. To use existing customized sshd_config, you need to copy it to %programdata%\ssh\sshd_config (Note that %programdata% is a hidden directory).
It’s robust, simple to install and use, and is compatible with various SSH clients, such as Bitvise SSH Client OpenSSH as well as PuTTY. It is a robust, easy-to-install, and user-friendly system. SSH Server is developed and is professionally supported by Bitvise. Additional protection may be provided by the system’s malloc/free application in the event that it detects double-free situations. Port forwarding is a method of forwarding TCP/IP connections from a remote computer via encrypted channels. Secure internet applications such as POP are protected with this. The service component consists of sshd and sftp-server and the ssh-agent.
It is able to work over organizational boundaries and is very efficient. SSH is an SSH protocol that is thought to be safe from security threats based on cryptography within the network if credentials and keys are appropriately maintained.
OpenSSH secures all data to prevent connections hijacking, eavesdropping, and various other threats. In addition, OpenSSH provides secure tunneling features and a variety of authentication methods and is compatible with all SSH protocols. It can be described as an SSH and telnet client, created by Simon Tatham for the Windows platform. PuTTY is free software that comes with source code. It is supported and developed by volunteers. This is the homepage of the SSH protocol software, the software, and other details. SSH is a program that allows secure system administration and file transfer over unsecured networks.
How to Get Openssh for Free
Take a look at Logging Facilities for options to switch to file-based logging. A rich command-line interface for many shells like bash, Powershell, and Cygwin (#1082 as well as #1211). Allow SSH connection when the machine’s name is identical to the username. It is a sign that a harmless program is incorrectly flagged as malicious because of an excessively broad detection signature or algorithm that is used in antivirus programs. OpenSSH can help you avoid attacks on your system’s security and allows users to transfer encrypted data through a network without cost. When the installation downloads, but fails to start, try the steps below.
This version allows the UpdateHostKeys option on default, to help clients by automatically moving to more efficient algorithms. The complete SFTP support is available by using the SFTTP command as the client, and the sftp-server subsystem to act as a server. Interoperability between different implementations is the desired goal however it is not a guarantee. As OpenSSH advancements continue old protocols, encryption methods important types, and other alternatives with been identified as having weaknesses are usually removed.
We also offer the SSH Client that runs on Windows that is not an exact copy of PuTTY It is however free and is maintained with a lot of dedication. Remote operations are executed by using ssh, SCP, and SFTP. The site was launched in March of 2014 by an ensemble composed of programmers and writers from Vietnam. The project currently is available in five languages, including English, French, German, Russian, and Vietnamese.
In Windows Server 2016, right-click the executable of the installer in Windows Explorer, click Properties and then check if there is a have to unblock it in the General tab. We are the developers of the SSH Server for Windows, that can be used with PuTTY. At times it is necessary to locate their PuTTY Download link. Key management is managed using ssh-add, keyscan, ssh key sign, and ssh-keygen. OpenSSH is the most popular connection tool to allow remote login via an SSH protocol.
Openssh System Requirements
- Operating System: Windows 7/8/8.1/10
- Memory (RAM): 512 MB of RAM required.
- Hard Disk Space: 100 MB of free space required.
- Processor: 1 GHz Intel or AMD processor.