Each vendor provides a degree of surveillance on devices that are registered and not monitored. It is commonplace to treat corporate-owned devices in a different way, even to having a minimum number of applications and limiting or removing the capability to install new applications. The most important concern for IT workers in the corporate world is protecting corporate data, and all of the apps we tested have this capability at some point. IBM MaaS360 fulfills all the essential features of a mobile-based management system and offers some additional features that you will not discover anywhere else other than Big Blue. There are some issues, however, such as the remote control feature requires the use of a third-party application.
Mobile Device Manager
Password 123
The products we evaluated offer integration with Microsoft’s on-premises AD service for authenticating corporate users. Microsoft Intune remains one of the top choices for managing devices for those operating in Microsoft-centric environments. The bundle options for Azure-based security and identity tools have gotten better and offer an extremely strong development direction. However, the cost is likely to be significant and for non-Microsoft operating systems There are a few under-appreciated capabilities as well. IT administrators today must monitor the ever-growing number of mobile devices on their networks. We examine eight apps that can assist administrators in knowing the resources that employees use on their mobile devices and find, lock, and even wipe them clean. Reduce the complexity of inventory, configuration, as well as management for your devices.
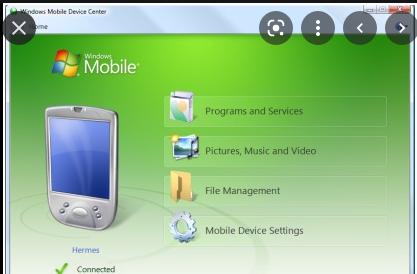
A comprehensive set of policies that cover an array of security options. Juniper Systems manufactures a variety of rugged tablets and handhelds that run Windows 10 and Android operating systems. Its Microsoft Windows Mobile Device Center allows you to establish new alliances, synchronize your content and manage images, music, and video on Windows Mobile-powered devices. Multi-layered security that doesn’t disrupt your business or users.
Together together with security for endpoints, it is easy to remove affected devices in the event of a security breach and then automatically push the software and then reconnect the device connected to the network. Make sure you allow your employees to work from any device knowing the security features are in place to secure corporate information across different endpoints.
Mobile Device Manager Features
The use of security based on policy is common in all the devices included in this review. Setting devices to utilize a personal identification number to secure the device is only one of many security policies that can be set to be obligatory. Other policies to limit behaviors or restrict access to particular apps are also popular. The boundaries become unclear when you go from devices owned by the company to personally owned devices, or in the BYOD scenario. If you’re unsure of what MDM or enterprise mobility management, as it’s commonly known as, well it’s been a little different from our previous roundup as well.
The application is compatible with a both touchscreen as well as touchscreen devices that aren’t touch-screen compatible. AppTec360 checks a lot of these boxes like other applications we’ve reviewed, but with a less appealing appearance.
Create profiles easily, apply restrictions, and establish and enforce security guidelines. Enterprise Mobility Management capabilities to effectively manage and protect the mobile devices within your organization.
Furthermore, the system requires the purchase of an additional product in order to allow remote control. We’d like to point out that occasionally we might overlook a potentially harmful software program. To keep delivering an uninfected catalog of programs and applications Our team has incorporated the Report Software feature in every catalog page. This feature transmits your feedback to us.
How to get Mobile Device Manager Free
It’s not difficult to see that a lost company mobile device poses a serious danger. The capability to track or lock and possibly wipe out lost devices should be readily available. A majority of the devices discussed here have geofencing capabilities that can create alerts and take actions in the event that a device crosses the boundaries of a particular area. This is great for companies that have an employee base in the local area where devices shouldn’t be beyond a specific distance from the office. This feature is adjustable to accommodate employees on the move and, in many instances, the time limit can be set also.
Each of these vendors has several additional capabilities above standard MDM to grab your interest. Controlling desktop computers is another aspect where conventional mobile-based management systems are seeking to gain traction. The adoption by companies of Windows 10 has provided an opportunity in this area and many of these vendors have offered the capability to support this in their products. 87% of professionals working in the field use a PC or at least a mobile device to perform their day-to-day tasks. Workers are no longer tied to their desktops at one place they are always in motion with a range of devices and accessing many different applications. With BYOD personal and business, devices must be controlled and integrated with the IT Management systems of the company. IT Management systems, without restricting access to personal information or security.
We do not support or endorse any use or usage of the software when it is in contravention of the laws. It is a program that Windows Mobile Device Center simplifies managing media on the Windows Mobile powered device and your personal computer.
Beware! This software program could be dangerous or could include unwanted bundles of software. Distribute and purchase AppStore applications easily with the Volume Purchase Program.
Mobile Device Manager System Requirements
- Memory (RAM): 1 GB of RAM required.
- Operating System: Windows 7/8/8.1/10
- Processor: Intel Dual Core processor or later.
- Hard Disk Space: 150 MB of free space required.