The numbers are consistent, however, which leads me to believe it’s coming from the cocoon. Other products offer privacy or security options, but not both. Cocoon bundles all of the features in one simple browser toolbar to provide total privacy online and protection. It’s hard to determine the validity of the claims on a non-initiative basis however, based on our tests it appeared to be promising. We were able to access geo-restricted websites, meaning that our location was concealed as well as we could not log in to websites without entering our login details, meaning that we weren’t cookie-free. Cocoon also claims to safeguard users from malware and viruses that you can pick up on the internet. Despite the huge advances in the field of security for browsers, the Internet is still an unintentionally risky environment for your privacy. Get More Softwares From Getintopc
Cocoon
Password 123
blocked is highly likely that this program is infected with malware or has unneeded software. Beware that this program may be harmful or could include unwanted packaged software. After having got my head around the easy to comprehend the concept, I’m not using this only to protect my internet. The free account must be registered and activated on getcocoon.com/signup to access Cocoon. Cocoon service. Cocoon can be described as an integrated Firefox browser extension that makes all your online activities secure, private, and safe from viruses.
Cocoon Features
The laws regarding usage of the program differ from country to country. We do not recommend or approve of any use of this software when it is in contravention of the laws. All your data is kept “in the cloud” and so is everything you do with Cocoon (bookmarks notes, bookmarks, and so on. ) is accessible wherever you sign into. Overall, Cocoon brings forth an array of helpful options for users who value privacy on their Internet privacy. It’s as user-friendly just like other Firefox browsers and its functions are available without any input on your side.
Today, you are monitored in a variety of ways that you’d never even imagined possible. Thus protecting your personal data and your computer from malicious malware when browsing the Internet is a matter of combining good habits of browsing and the use of specialized software. To check the SHA512 signature in the files, it is necessary to run a program known as sha512sum. It’s included in a variety of Unix distributions. This means that a legitimate program is flagged incorrectly as harmful due to an excessively broad detection signature or algorithm that is used in antivirus programs. In addition, the browser is simple to use as a contemporary browser.
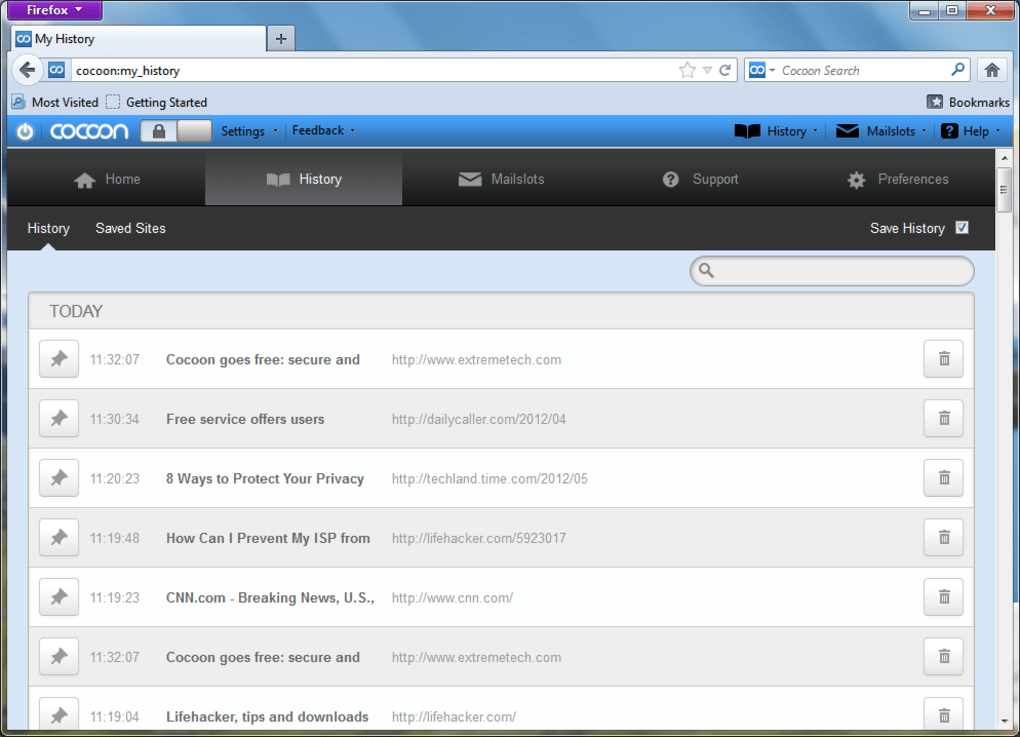
When you’ve downloaded Cocoon after restarting Firefox after that, you’ll have to create an account however, it’s a breeze. You can log in to the Cocoon accounts from any device or any other location, as long as your browser supports the Cocoon software installed, however, you’ll only be able to log in to your account via only one computer at a.
The cocoon protects your privacy and security wherever you surf the internet. Simple web-based application built on Cocoon 2.2 which makes use of blocks and servlet-based services. The best method to become acquainted the Cocoon 2.2 and how to utilize it along with Maven 2 is the Getting Start tutorial. If you take that route, Maven 2 will take the responsibility to download all dependent dependencies. If you have Family Sharing enabled Up to six family members are able to make use of the application. Location This app can track your location even if it’s not in use this can affect the battery’s time. For more details, refer to the privacy policy of the developer.
Explore our archive of distributions or download the most recent Cocoon distribution by clicking from the options below. It is recommended to test the integrity of distribution files. CleanIt’s highly likely that this program is safe. The tool was created to serve the purpose of making it easier for the user to establish forwarding rules on his router. Cocoon is an easy-to-use and discrete app that keeps you as completely private and safe as you can when working online. Find trackers and limit their ability to monitor your online activities.
How to Get Cocoon for Free
We strongly suggest you check the integrity of downloaded files by using each of PGP as well as MD5. It is not advised to create a new program using one of them. Cocoon 2.2 was split up into blocks that are smaller in size. Anything that is beyond what Cocoon offers as its primary modules can be available in blocks. To get an overview of which blocks are available, check out this list. It is a good idea to check the authenticity of the files used for distribution.
No preferences for caches I like Cocoon to not be able to remember anything and what’s the purpose, I don’t like history, nor “junk.” Unfortunately, I’m looking for options to cache. Keep in mind that using Cocoon will affect many options in Firefox even after it’s removed. While the extension was helpful during our time using it, we experienced difficulty getting things back to normal after we had finished. Download.com is removing the direct download link after the request of the publisher and has made this page available to users for informational only.
Download.com has removed its direct download link and is offering this page solely for informational purposes. By signing up to Download.com you accept our Terms of Service and accept the practices regarding data that are described in the Privacy Policy. There is, however, an Getting Started package that contains an easy Cocoon 2.2 built-in application that utilizes Apache Ant as a build system.
However, you don’t need to do anything in order to use Cocoon simply begin surfing. We entered some search terms within Cocoon’s Cocoon Search field, which is secure to search using Google however we can switch the search engine in the direction of Bing or Yahoo through Cocoon’s online settings page. It’s not a secret that Cocoon will slow your browsing speed a bit but we’ve not tried an internet proxy that did not. Its performance is not that bad, however, and definitely not enough to be able to ignore its security, particularly when you are using an access point that is public.
The browser ensures that all of your personal information, from browsing history, to credit card numbers, social security numbers or bank passwords, usernames, and bank passwords, will be as secure as it is. It provides protection against online tracking, identity security as well as credit card protection and also hides your IP address. We’d like you to know that occasionally we could overlook a potentially harmful software program.
Cocoon System Requirements
- Operating System: Windows 7/8/8.1/10.
- Memory (RAM): 512 MB of RAM required.
- Hard Disk Space: 50 MB of free space required.
- Processor: Intel Dual Core processor or later.