The quick answer is that Two-factor authentication is in use regardless of whether that other authentication method “you have” comes from your smartphone, tablet, or the desktop application installed on your laptop. For instance, RSA Security, the leading provider of Two-Factor authentication, has a desktop app that has been successfully used in some of the biggest and most secure companies around the world. What is important is that it’s something that only you have access to. But, there is an enormous security benefit by running both from the exact same gadget. The majority of attacks that we encounter at present on our customers are sophisticated real-time phishing attacks. In these attacks, victims are sent via a fake email, or by some other method to a fake website that appears and feels similar to the genuine website.
Password 123
Authy
BlockedIt’s very likely that this program is infected with malware or has unneeded software. This program may be dangerous or could contain unwelcome bundles of software. We recommend this as a precaution in case your access is cut off to a device, you have another application that you can use you can log into your applications.
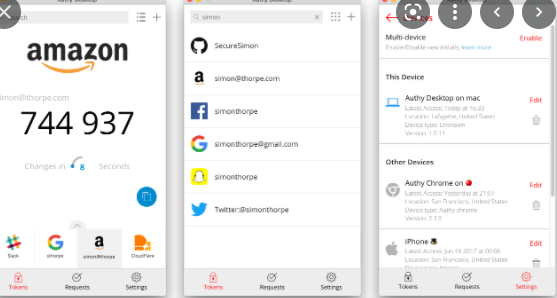
It’s a legitimate problem, but this is also true about the security of your RSA secure token, or even your smartphone. Two-factor authentication wasn’t created to safeguard against the theft of your device. There are a variety of other security tools that are intended to guard against this, like full disk encryption. We are happy to announce the public beta of the brand new Authy Desktop. It is a standalone desktop 2FA application that works on the two platforms of macOS or Windows and doesn’t rely on any particular browser. We also used the chance to create a fresh UI that lets you view your 2FA accounts in a list or grid view, and also the addition of a search bar that allows you to find accounts quickly. These features will eventually make it into our mobile apps, too.
This means that a legitimate program is incorrectly flagged as harmful due to an unwieldy detection signature or algorithm in an antivirus. If you’d like to, you can turn on the password-free sign-in option by using the Microsoft Authenticator application. You’ll have to verify your login again prior to entering the page for security settings in the event that you haven’t visited the page in the past. Be sure to go beyond the password and ensure that you are safe from account hijacks and hackers. Based on our scanning software, we’ve found that these flags could be believed to be genuine positives. Based on our scanner software, our team has concluded that these flags may be false positives.
Authy Features
Two-factor authentication is the best protection against unauthorized employees, which is why this product is suitable for both office and home use. The attacks are well-crafted that even the best users were tricked. And today, we’re making the first step towards eliminating phishing attacks. When you are able to log into a website the browser will store locally the unique identifier of your session, which is known as the session cookie.
If you’ve used Authy on your phone, Authy for Desktop works exactly the same way as Authy mobile application. If you don’t have an iPhone, this app offers a more efficient alternative to text messages as well as calls to the phone, and we believe you’ll be delighted with it.
CleanIt’s very likely that this program is safe. To add the account you have to Authy you must click on “Set up Identity Verification App on the page for additional security choices. Protect yourself from cyber-criminals and prevent accounts from being taken over by hackers with better security for no cost! Check out the following video clip to find out more about the reason to make sure that your accounts are protected with 2FA. 2FA is by far the most secure option to ensure your security online.
The cookie is used to inform the site of subsequent requests that you’ve already signed in so that the site won’t require you to sign in to the site to sign in again. This basically means that there’s no reason for malware to access your credentials or two-factor tokens when it’s possible to simply take your authenticated sessions. This was a modified version of our well-known 2FA application, which ran as an application within Chrome. Chrome browser. It had been extremely successful but many users were asking us to let them run Authy on their desktops without installing Chrome.
How to get Authy Free
When a user visits the fake website and is tricked to enter the login credentials of his account, which includes the two-factor authentication token which is then granting an account. In the case of Authy for Desktop, we’re taking things an extra step to provide two-factor authentication a seamless experience and give the power and security of secure authentication to users wherever, anytime. We acknowledge that the vast majority of people don’t utilize these safeguards which is why we have integrated encryption into our application. Authy for Desktop makes it easy for you to encrypt your local accounts using a master password – simply enter a password and we’ll take care of all encryption/decryption for you. The password also prevents your access to the app when you’re at home, by automatically encrypting your accounts. It also shields you in the event that your laptop gets lost or stolen. It is normal to log into your accounts using your laptop or desktop computer do you not?
Authy is simple and secure two-factor authentication accessible as a no-cost desktop or mobile application via Twilio. To obtain your Authy account simply click on the download link on the right side of the screen. The Authy App for desktop provides an easy and efficient method to gain access to your two-factor tokens quickly easily and safely using your laptop or desktop. We’re creating some truly innovative technology to resolve this issue. We’ll soon also keep the blacklist of known scam websites (updated on a regular basis) that will protect our customers and users from becoming victims of this type of attack.
Authy allows you to make use of “something you know” paired with “something you have” to securely log into your accounts by using two-factor authentication. In the past the only thing is “have” was either your phone, your smartphone, or tablet. Authy is a program that allows users to have additional security.
The laws regarding usage of the program differ from country to country. We do not recommend or approve of using this software in the event that it violates any of the laws. And after that, select “Set up a new Authenticator app’ on the following screen.
Authy System Requirements