This method can be used to block from external calls for your .NET class library, as and calls to methods defined in assemblies designed by your organization and used inside an obfuscated system. Obfuscation could cause problems when using reflection API in an obfuscated system. To avoid these issues, Agile.NET obfuscator fully supports Microsoft’s declarative attributes for obfuscation. These attributes, when declared directly in source code allow the user to specify the names of methods and classes which shouldn’t be changed. Agile.NET Obfuscator can rename the metadata of all constructs, which includes namespaces, classes name, methods signatures, and fields, along with methods’ implementation as well as the string values in your code. Renaming scheme that includes ‘unreadable chars scheme. This technique transforms classes, methods, and field names into unprintable character strings that are Unicode. If decompiled, the result will be very difficult to comprehend source code.
Password 123
Agile.Net Obfuscator
Join our rapidly expanding customer base that includes thousands of customers who use Agile.net every day to secure their applications running using .NET Core 3.1, .NET 2.0 and above Windows, WinRT, WP7 Windows Platform 8 Compact Framework 2.0 and up and as well as ASP.
It is also a way to make large libraries simpler to manage. could otherwise comprise several DLLs that need to be linked from the project that is using the library. Merging decreases the overall size of the installation and reduces load speed since the windows loader isn’t required to load many DLL files. It is vital that an obfuscator preserve its functionality fully intact while rendering the original source code completely unrecognizable when the obfuscated code is decompiled. Agile.NET Obfuscator guarantees that the obfuscated program runs the same way it did in the initial assembly. In order to achieve this, it is necessary to save a map file. be saved and then employed to guarantee that the change has been maintained in the event of making changes, and then release the obfuscated assemblies. Renames external references, thus significantly increasing the number of constructs renamed.
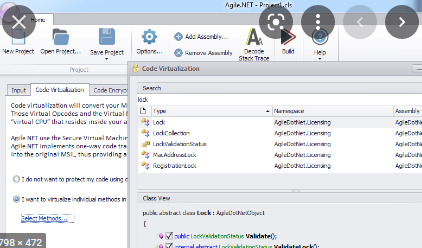
Agile.NET obfuscator provides control overflow obfuscation. Control flow obfuscation conceals the information regarding control flow in the program by changing exiting code flow patterns into semantically similar constructs, yet distinct from the original code written. This control flow decryption process transforms the original code into spaghetti code making it difficult to deduce the logic behind the program. Agile.NET .NET obfuscator ensures that the code flow of the obfuscated component remains unchanged. Agile.Net Obfuscator is a mighty tool for protection and application for .NET software and Licensors. Apart from changing metadata names, this program employs obscure, advanced methods which make the overall protection strategy more complicated and involve full reverse engineering. These metadata comprise namespaces classes, names for classes, signaling strings, signaling, and many more. This can be used to alter the flow of code of the program through the transformation of existing patterns of code flow into semantically similar constructs, yet different from the code originally written.
Agile.Net Obfuscator Features
Because unprintable characters are utilized, it isn’t possible to compile the code following decompilation. One of the repercussions of obfuscation can be the difficulty of debugging code with obfuscated syntax. The exceptions recorded by users are usually accompanied by obfuscated method and class names, making it difficult to locate the stack trace back to your source code. Agile.NET Obfuscator produces maps clearly labeled with a full description of the entities obfuscated as well as their original names. the information will assist the user to understand the output of the debugger from the obfuscated assemblies. Apart from changing the name of your metadata objects It also provides advanced obfuscation strategies that make your overall security scheme more robust and block reverse engineering completely. Cross Assembly Obfuscation permits renaming external references, thereby dramatically increasing the amount of obfuscated objects. If you have a set of assemblies that communicate with each other, Agile.NET will rename classes methods, fields, and methods that are referenced by other assemblies in a uniform manner.
For example, if class A is declared within assembly A gets referenced by assembly B, and Agile.NET transforms the class A name in A1 it’ll name B’s external reference of A too. An attacker of this kind will typically browse the assemblies that are deployed for strings that contain words like “GetLicense” or “Invalid Licence’. In locating these strings, hackers try to bypass the license protection included in the software they hack. In locating these strings, hackers try to circumvent the licensing protection that is embedded in the program they are hacking. Agile.NET transforms the strings in the source code to encrypted strings. The strings are decrypted automatically as they are required. This is a great way to combine an executable file and its supported dynamic linked libraries that enable you to share a running program in a single file.
How to get Agile.Net Obfuscator Free
Agile.NET assures that the code flow in the obfuscated assembly is maintained. Obfuscates all aspects of your code, such as names for methods and classes user strings, managed resources methods implementation, and system as well as a library call. Agile.net safeguards more of your application than another obfuscator, because it knows what can be changed and what should be left in place. The actual calls are made by using the metadata token of the method instead of the method’s title This makes it more difficult to understand the program’s logic since it’s no longer possible to look through the code with traditional reflector tools.
For example, if class A as assembly A has a reference by assembly B, and Agile.NET transforms the class A name into A1, the program will change the external reference of B’s between A and A1. Once the assembly is loaded, Agile.NET connects with its .NET runtime engine and handles decrypting the MSIL on a per-method basis. Agile.NET creates an environment running MSIL code from the beginning. MSIL code, decrypting just one method at a time. this crucial feature reduces the risk of exposing MSIL code to memory and keeps the code out of physical memory. Transform MSIL code in .net core assemblies into native code, eliminating MSIL code completely and offering native code security. Code virtualization transforms all of your MSIL codes into Virtual Opcodes that will only be comprehended by a secured Virtual machine.
Agile.Net Obfuscator System Requirements
- Memory (RAM): 512 MB of RAM required.
- Operating System: Windows XP/Vista/7/8/8.1/10.
- Processor: Intel Dual Core processor or later.
- Hard Disk Space: 30 MB of free space required.